After finally receiving the documents I was waiting for I can write a detailed essay about the compromise of Soviet codes in WWII. Within the month I’ll also try to cover other interesting cases such as the German investigations on the solution of the Enigma by the Polish codebreakers and the FLD code used by French War Ministry in the period 1939-1940.
Upcoming essays
↧
↧
Update
I have uploaded TICOM report DF-176 'Answers written by professor doctor Wolfgang Franz to questions of ASA Europe' - 1949. Acquired through the NSA’s FOIA office.
Available from my Google Docs and Scribd accounts.
↧
Professor Wolfgang Franz and OKW/Chi’s mathematical research department
Nazi Germany had several codebreaking agencies both military and civilian. The armed forces had separate agencies for the Army, Navy and Airforce plus there were codebreaking departments in the Foreign Ministry, in Goering’s Forschungsamt and in the Supreme Command of the Armed Forces. This last department operated on civilian lines even though it was subordinated to the military.
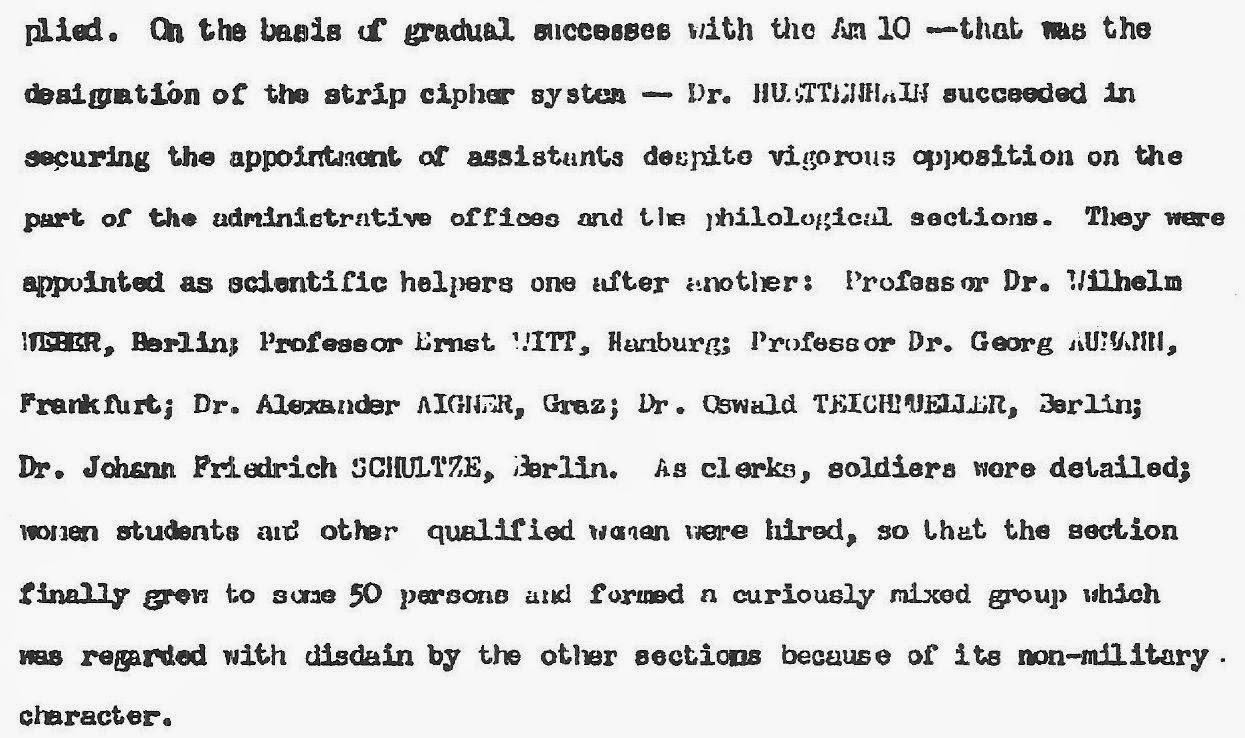
Thanks to the success of the department is solving the strip cipher dr Huettenhain was able to hire more mathematicians and expand the research section.
It is interesting to note that a special cryptanalytic device called the ‘Tower-Clock’ was used to solve the strip system. Franz says in pages 9-10:
‘In addition, there was built at my suggestion at the Bureau an electric machine which permits determining a number of repetitions of letters in a polyalphabetic substitution on a width of 30 with a depth of 20 to 80 lines, taking one line at a time, which naturally is fundamental for problem (f) above.’
The apparatus consisted of a single teleprinter tape reading head (speed 1 1/2 symbols per second); a storage means, by which any one of five different scores could be assigned, on a basis of frequency, to each of the letters in the 30 separate monoalphabets that resulted from the 30 columns of depth; a distributor that rotated in synchronism with the tape stepping, and selected which set of 30 scores was to be used as basis for evaluating the successive cipher letters; and a pen recording device.
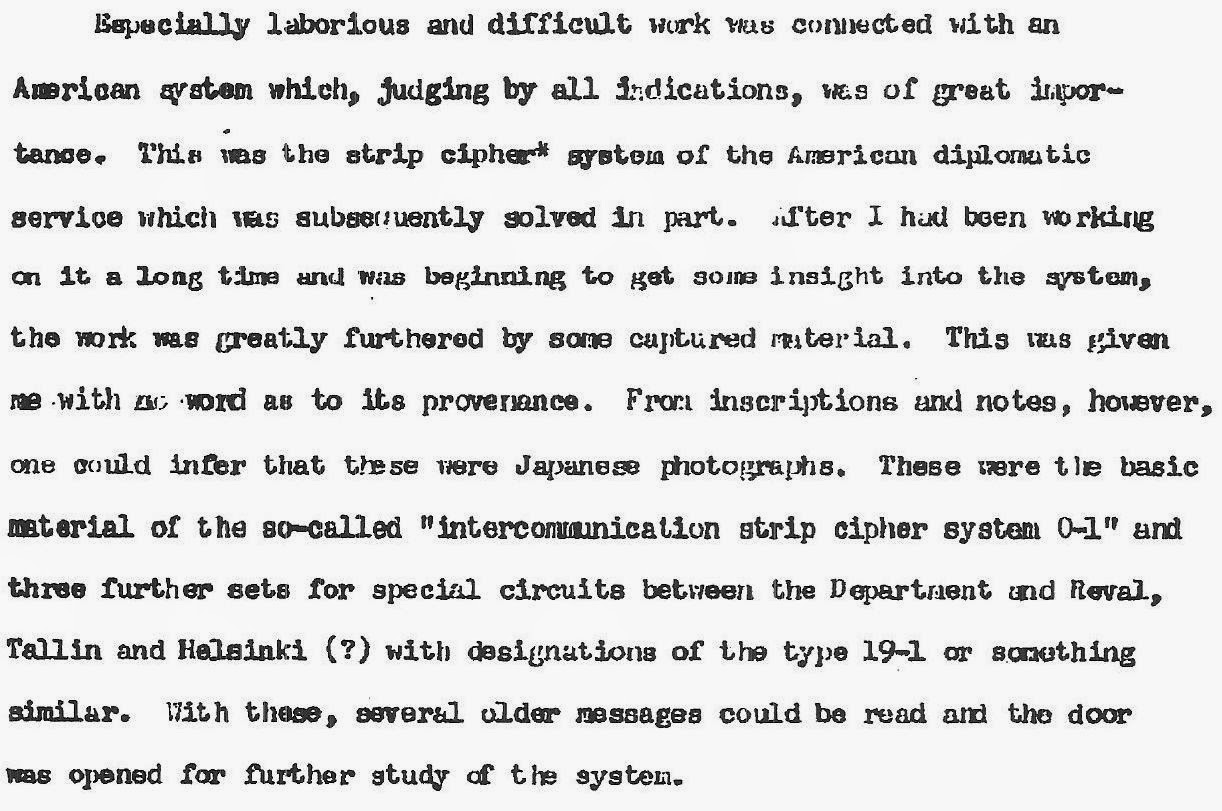
The German codebreakers were only able to exploit the strip cipher to such a degree thanks to serious mistakes in the use of the system by the State Department. Franz acknowledged this in page 6 of the DF-176 report:
The OKW/Chi agency
OKW/Chi - Oberkommando der Wehrmacht/Chiffrier Abteilung was the Signal Intelligence Agency of the Supreme Command of the Armed Forces. It had been established as a separate agency in 1920 and in the interwar period it was able to solve the codes of many foreign countries. Initially the focus was on philological research but the introduction of more complex codes and ciphers led the Germans to invest in mathematical research in the field of cryptanalysis.The person who orchestrated this change in priorities was Wilhelm Fenner. Fenner started working for the department in 1921 together with his friend Fedor Novopaschenny, a former Tsarist codebreaker and in 1922 became an official employee. In the beginning he didn’t know much about solving codes but he learned mathematical techniques from his Russian friend and came to realize that the agency would need to make organizational changes in order to solve the more difficult foreign cryptosystems.
Since Fenner quickly became head of the cryptanalysis department he was able to carry out his plan to reorganize the agency. First he introduced a more rigorous training program for analysts and concentrated on the scientific analysis of cryptologic history and systems.The next step in the 1930’s was to hire mathematicians.
Professor Huettenhain and OKW/Chi’s mathematical research departmentThe first mathematician hired by Fenner was Erich Huettenhain. In the mid 1930’s Huettenhain worked at the observatory of the University of Münster and came to Fenner’s attention when he contacted Chi with some of his proposals for cryptographic systems. Although his systems were ‘unusable without exception’ he was offered a job at Chi and he accepted.
Huettenhain became responsible for mathematical analysis of more difficult cipher systems and in the early years of WWII new personnel were hired to form a separate mathematical research department.These were Wolfgang Franz, Werner Weber, Ernst Witt, Georg Aumann, Alexander Aigner, Oswald Teichmueller and Johann Friedrich Schultze.
During the war they solved several difficult foreign cipher systems. Weber was successful with a Japanese diplomatic code transposed on a stencil, Witt solved the stencil subtractor frame used by the Polish diplomatic and intelligence service and Franz was responsible for the exploitation of the State Department’s strip cipher.
Apart from the aforementioned individuals, two more mathematicians, Karl Steinand Gisbert Hasenjaegerwere hired to work in the cipher security department. Professors Franz and the State Department’s strip cipher
According to the recently declassified TICOM report DF-176 ‘Answers written by professor doctor Wolfgang Franz to questions of ASA Europe’ Wolfgang Franz primarily studied mathematics in the period 1924-1929, during 1930-1934 worked as an assistant at the mathematical seminar at the University of Marburg and in 1937 moved to the University of Giessen as an assistant. When at the beginning of WWII the University of Giessen was closed down he spent a semester as a substitute at the University of Gottingen. Franz’s area of expertise was topology.
Thanks to a friend of his who knew Huettenhainhe was able to get assigned to the OKW Cipher department in Berlin in 1940. The initial training program consisted of solving simple codes and ciphers and as Franz was easily able to cope with these he moved on to real traffic.The first systems he worked on were a Mexican and a Greek code and he was able to solve them. The most important system solved by Franz was the US diplomatic M-138-A strip cipher, called Am10 by the Germans:
‘Especially laborious and difficult work was connected with an American system which, judging by all indications was of great importance. This was the strip cipher system of the American diplomatic service which was subsequently solved in part.’According to DF-176, p6 Franz had started his own investigations into this system and was able to make some limited progress when he received the ‘circular’ strips 0-1 and three ‘special’ strips used between Washington and Helsinki, Tallinn and Reval. Using these strips messages could be solved and his investigations could move forward.
Regarding the strip cipher 70 ‘different traffics’ (links?) were identified and 28 solved plus 6 numerical keys.
‘In addition, there was built at my suggestion at the Bureau an electric machine which permits determining a number of repetitions of letters in a polyalphabetic substitution on a width of 30 with a depth of 20 to 80 lines, taking one line at a time, which naturally is fundamental for problem (f) above.’
According to EASI vol2 ‘Notes on German High level Cryptography and Cryptanalysis’ , p56-57
c. Statistical "depth-increaser." - The "Turmuhr," or "Tower-Clock was a device for testing a sequence of thirty consecutive cipher letters statistically against a given "depth" of similar sequences, to determine whether the former belonged to the given depth. It was used "primarily for work on the U.S. strip cipher, when cribbing which was generally employed was impossible. It cost approximately $1,000.00.The apparatus consisted of a single teleprinter tape reading head (speed 1 1/2 symbols per second); a storage means, by which any one of five different scores could be assigned, on a basis of frequency, to each of the letters in the 30 separate monoalphabets that resulted from the 30 columns of depth; a distributor that rotated in synchronism with the tape stepping, and selected which set of 30 scores was to be used as basis for evaluating the successive cipher letters; and a pen recording device.
The German codebreakers were only able to exploit the strip cipher to such a degree thanks to serious mistakes in the use of the system by the State Department. Franz acknowledged this in page 6 of the DF-176 report:
‘This strip cipher system, when rightly employed, doubtlessly has great advantages .It appears to me, however, that it was not used with sufficient caution. Only through carelessness, in part through lack of care in setting up, was it possible to break into the system as far as we did. Only after the Americans had obviously noticed that many of their messages were being read was the application so modified that although the basic idea was the same the possibilities of breaking in were materially reduced.’
Postwar career
In the postwar period professor Franz returned to teaching at Frankfurt University where he eventually became dean of the newly established Department of Mathematics. Also in 1967 he became president of the German Mathematical Society.In the end It might give some comfort to the Americans to know that their strip cipher was solved by a real gentleman, as report DF-176 says: ‘Personal contact with Dr Franz indicated that he was a gentleman of unusual scholarship and integrity, an impression confirmed by the report’.
Sources: TICOM reports DF-187 A-G and DF-176, ‘European Axis Signal Intelligence in World War II’ vol2
↧
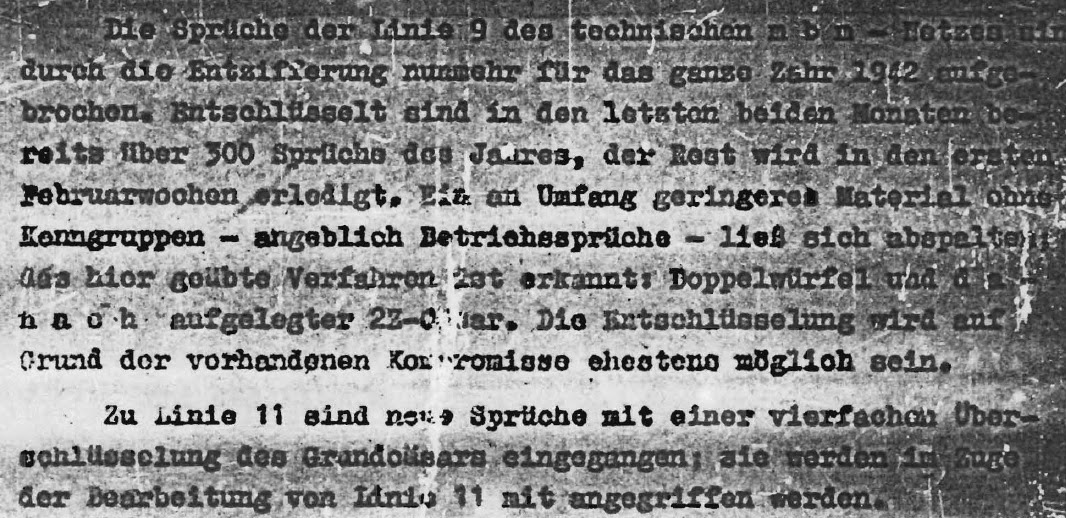
Case ‘Wicher’ – Information from the war diary of Inspectorate 7/VI
In the Second World War the Allies and the Axis fought battles not only with tanks, aircraft and infantry but also in the fields of signals intelligence and cryptology. Both sides tried to protect their communications from outsiders by using complicated cipher procedures and their codebreakers made every effort to solve enemy codes and thus gain valuable intelligence.
At the same time there are a few references to case ‘Wicher’ in the war diary of Inspectorate 7/VI but I haven’t been able to locate any actual reports. It should also be noted that the German cryptanalysts involved in these investigations were not interrogated after the war, so we do not have their side of the story.
German investigations and information from the War Diary of Inspectorate 7/VI
During the war representatives from the German cipher departments and the military intelligence service Abwehr had meetings on case ‘Wicher’. Although ‘Der Fall WICHER’ says in page 9 that the Naval High Command – OKM did not know about the Polish affair the war diary of Inspectorate 7/VI for the month of April 1942 shows that a meeting took place between the Naval officers Stummel and Singer, the Abwehr officials Dr Schneider and a captain and the Army cryptanalyst Dr Pietsch.
The report says that the naval officers wanted closer cooperation between their department and the Army’s on the Enigma investigations.
The only other reference I’ve found is in September 1943 when Dr Schneider, the OKM’s Captain Singer and Inspectorate’s 7/VI Dr Pietsch visited the Neuengamme concentration camp (near Hamburg) and interrogated the Polish intelligence officer Leja. A report was issued but I’m afraid I don’t have it.
After the fall of Poland a few Polish codebreakers were able to reach France and started working for the French signals intelligence organization (codenamed PC Bruno), commanded by Gustave Bertrand. After 1940 this unit changed name (codename Cadix) and location and continued to monitor and decode some German communications, including a few Enigma keys (6). ‘Der Fall WICHER’ says in page 5 that ‘The French cryptanalyst Bertrand was arrested and interrogated at this time, but he did not disclose the ENIGMA work, and it is very likely that he did not know what was happening in England and America on the problem’. This might not be entirely accurate as ‘the book Enigma: The Battle for the Code’, p319 says that in January 1944 ‘Gustave Bertrand is arrested by the Germans while working under cover for the Resistance in France. He admits to himself that he will not be able to remain silent if he is tortured, so, in order to obtain the chance to escape, he agrees to collaborate with the Nazis‘.
The Anglo-Americans were able to gain information of great value from reading their enemies secret communications. In Britain the codebreakers of Bletchley Park solved several enemy systems with the most important ones being the German Enigmaand Tunny cipher machines and the Italian C-38m. Codebreaking played a role in the Battle of the Atlantic, the North Africa Campaign and the Normandy invasion. In the USA the Army and Navy codebreakers solved many Japanese cryptosystems and used this advantage in battle. The great victory at Midway would probably not have been possible if the Americans had not solved the Japanese Navy’s code.
However the Axis codebreakers also had their successes and they were also able to compromise various Allied crypto system both low and high level.One interesting question that often comes up in history books is whether the Germans ever suspected that their Enigma cipher machine was being read by the Allies and how the war could have taken a different turn had they managed to discover that it was not secure.
The truth is that the Germans never considered the Enigma to be unbreakable and in fact they had discovered in 1939 that the Poles had solved messages. During the war they continued to investigate the Polish solution of the Enigma, which they called case ‘Wicher’. (1)The plugboard Enigma and the German armed forces
The Germans adopted a modified version of the commercial Enigma machine as their main cipher system in the 1930’s. The modification they introduced in the commercial model was a plugboard. This vastly improved the cipher security of the Enigma device.In 1934 the Army and Navy agreed to use the plugboard Enigma as their main cipher system and in 1935 the Airforce followed (2). At the start of WWII Germany was the only country in the world to use a cipher machine for all its mid and high level traffic.
During WWII tens of thousands of Enigma machines were used by the Germans. It seems that no one knows for sure how many Enigma machines were built however a good estimate, based on their serial numbers, is that more than 40.000 were constructed. (3)The Germans used the Enigma extensively and they were always worried about the security of their main cipher system. Their cryptologic security departments, scattered across their cryptologic agencies, researched ways to break the Enigma and based on their observations changes were made in operating procedures. Although it is often claimed that they considered the Enigma to be unbreakable the truth is that they constantly upgraded its security, both with physical modifications and with new, more secure cipher procedures.
One of the reasons that they improved the Enigma during the war was that they had learned that in the prewar period the Polish codebreakers had been able to solve messages.The Polish solution of the Enigma in the 1930’s
In the 1930’s the rise of Hitler’s National Socialist German Workers' Party led to German rearmament and a more aggressive foreign policy. This change in policy alarmed European nations and especially in neighboring Poland there was a great need to keep a close eye on the military developments in Germany. The Polish state had limited resources but the intelligence service operated efficiently and was able to gather valuable intelligence against the main Polish enemies which were Nazi Germany and the Soviet Union. The Poles had a tradition in the field of cryptanalysis as their codebreakers had contributed to the defeat of Soviet troops in the war of 1919-1921by solving the codes of the Red Army.
In the early 1930’s the Polish cipher bureauconcentrated on the solution of the widely used Enigma cipher machine and for this reason hired three young mathematicians: Marian Rejewski, Henryk Zygalski and Jerzy Różycki. Thanks to cipher material obtained through Francethese codebreakers were able to solve the plugboard Enigma and read German messages. In this task they succeeded where the French and British codebreakers had failed!German indicator procedures and the ‘Grundstellung’
The Polish solution was based on the German indicator procedure. Each Enigma network had its own settings which changed monthly, up to October 1936 when they were changed each day. The key list specified which rotors would be used and their position in the scrambler unit, the ring settings on the rotors and the plugboard settings. In addition the keylist specified the Grundstellung (basic setting) for the network. This was the position of the rotors used to encipher the indicator of each message. The indicator specified the starting position of the rotors which was different for each message. The way the system worked was that the Enigma operator had to set up the machine according to the instructions of the keylist and then had to select a random starting position for the 3 rotors for each message. This position was communicated to the other party after doubly enciphering it on the basic setting.
So let’s imagine that a cipher clerk has set up his Enigma machine according to the daily settings and is ready to encipher a message. He turns the rotors of the machine at random and stops when they are at WJS, which will be his ‘message key’. With the wheels at WJS he starts typing out the message and the cipher text is written down by another clerk. In order to send this message to another party he needs to add at the beginning of the message the enciphered indicator so the operator who receives it will know to set his machine rotors at WJS. The procedure used up to May 1937 (for the Navy) and September 1938 (for the Army and Airforce) was to take the initial position of the rotors for the message (in our case WJS) and encipher it twice in succession at the Grundstellung/basic setting. So in our example the cipher clerk would have to set the Enigma rotors to the network’s Grund setting, let’s say KJW and type WJS twice. Let’s assume that the output is HCE VKR. These 6 letters would be placed at the start of the message as the indicator. Then the cipher clerk who received the message would turn his rotors to the Grund setting KJW and type HCE VKR, which would give him WJS WJS. Thus he would know that the message key is WJS and he would be able to decipher the message.The Polish codebreakers were able to exploit the use of a Grund setting and the double encipherment of the message key. The flaw in this procedure was that there was a connection between the first and fourth, second and fifth and third and sixth letters of the indicator. It is obvious that these letters represented the same initial letters of the message ‘key’ at three stages apart. Using mathematical theory the Polish mathematicians were able to recover the Enigma settings and the messages keys so they could decode the radio traffic.
However in the late 1930’s the Germans upgraded the security of the Enigma by modifying their operator procedures. In May 1937 the Navy introduced an indicator book and encipherment tables for the indicators thus defeating the Polish method. In September 1938 the Army and Airforce abandoned the use of the Grundstellung and each Enigma operator had to choose a random starting position as the message key and encipher it twice at another random position. In our example instead of KJW the operator will choose another rotor position, let’s say JME and encipher the message key WJS twice thus giving KDB CUJ. The indicator sent with the message will be JME KDB CUJ. The receiving party will set their Enigma at JME and type KDB CUJ, giving WJS WJS which will be indentified as the message key.Although the German Army and Airforce abandoned the Grundstellung they continued to encipher the message key twice thus allowing the Poles to compromise this new procedure. However the Polish operation would finally end in December 1938, when two more Enigma rotors were issued (making a total of 5), as the Polish cipher bureau did not have the resources needed to overcome this setback.
The greatest contribution of the Polish codebreakers to the Allied cause came in July 1939 when their officials revealed to British and French codebreakers that they had been solving the Enigma for years and shared their method of attack. This breakthrough allowed the Franco-British alliance to solve some Enigma traffic in the period 1939-1940 and made it possible for Bletchley Park to avoid a costly and time consuming attack on the Enigma. Der Fall Wicher
In September 1939 Germany invaded Poland and after a brief period of fighting was able to defeat its armed forces and occupy the country. The Polish cipher burau was based in an area south of Warsaw and was evacuated before the German troops arrived but it seems that not all of their documents were properly disposed of. When the Germans examined the area they were able to find documents pointing to a very secret department in the cipher bureau, unusually large payments made to mathematicians and translations of messages thought to have been sent on the Enigma machine (4). This information obviously alarmed the German officials and during the war they made efforts to locate and interrogate Polish officials that might know more about the Enigma compromise. The German called this investigation case ‘Wicher’ (der fall Wicher).
Unfortunately the information we have on their investigations is very limited and often contradictory. The NSA article ‘Der Fall WICHER: German Knowledge of Polish Success on ENIGMA’ by Joseph A. Meyer has a summary of the information from various TICOM reports but some of the statements made are not correct. At the same time there are a few references to case ‘Wicher’ in the war diary of Inspectorate 7/VI but I haven’t been able to locate any actual reports. It should also be noted that the German cryptanalysts involved in these investigations were not interrogated after the war, so we do not have their side of the story.
German investigations and information from the War Diary of Inspectorate 7/VI
According to ‘Der Fall WICHER’ and various TICOM reports (5) in 1939 the Germans were able to find incriminating evidence left behind by the Polish codebreakers when they evacuated their headquarters. It seems that the plaintext versions of a few Enigma messages were found thus showing the compromise of the cipher machine. Unfortunately I don’t have the 1939 and 1940 reports of the German Army’s codebreaking agency Inspectorate 7/VI, so I can’t say whether more information can be found there.
In any case the Germans after researching the security of the indicator procedure seem to have discovered on their own that the double encipherment of the indicator was a risk and in May 1940 it was changed. From then on the cipher clerk chose a random message key and enciphered it on another random setting only once. In our previous example this means that instead of sending the indicator JME KDB CUJ, only JME KDB would be sent.Since the Polish solution was based on the double encipherment of the indicator this change defeated their method. From then on the codebreakers of Bletchley Park had to employ their own method of solution which was based on the use of ‘cribs’ (suspected plaintext in the ciphertext) and high-speed cryptanalytic equipment called ‘bombes’.
However there is no indication that this indicator change was implemented due to the ‘Wicher’ case. A German Army cryptanalyst named Buggisch said in TICOM report I-92‘Final Interrogation of Wachtmeister Otto Buggisch (OKH/In 7/VIand OKW/Chi)’, p5 that the change came as a result of standard security studies:During the war representatives from the German cipher departments and the military intelligence service Abwehr had meetings on case ‘Wicher’. Although ‘Der Fall WICHER’ says in page 9 that the Naval High Command – OKM did not know about the Polish affair the war diary of Inspectorate 7/VI for the month of April 1942 shows that a meeting took place between the Naval officers Stummel and Singer, the Abwehr officials Dr Schneider and a captain and the Army cryptanalyst Dr Pietsch.
Another reference to case ‘Wicher’ can be found in July 1942 when the aforementioned Dr Schneider together with the department head of Inspectorate 7/VI visited imprisoned Polish intelligence officers who had served in the General Staff. The report says that the results were meager as some of those that the police had arrested were the wrong people and those that were interrogated either did not volunteer information or had such a low position that they did not know anything of value. The only admission made by the Poles was that they had solved the hand cipher used by the German Army and Police.
The only other reference I’ve found is in September 1943 when Dr Schneider, the OKM’s Captain Singer and Inspectorate’s 7/VI Dr Pietsch visited the Neuengamme concentration camp (near Hamburg) and interrogated the Polish intelligence officer Leja. A report was issued but I’m afraid I don’t have it.
After the fall of Poland a few Polish codebreakers were able to reach France and started working for the French signals intelligence organization (codenamed PC Bruno), commanded by Gustave Bertrand. After 1940 this unit changed name (codename Cadix) and location and continued to monitor and decode some German communications, including a few Enigma keys (6). ‘Der Fall WICHER’ says in page 5 that ‘The French cryptanalyst Bertrand was arrested and interrogated at this time, but he did not disclose the ENIGMA work, and it is very likely that he did not know what was happening in England and America on the problem’. This might not be entirely accurate as ‘the book Enigma: The Battle for the Code’, p319 says that in January 1944 ‘Gustave Bertrand is arrested by the Germans while working under cover for the Resistance in France. He admits to himself that he will not be able to remain silent if he is tortured, so, in order to obtain the chance to escape, he agrees to collaborate with the Nazis‘.
The same source, ‘Enigma: The Battle for the Code’, p319 says that in March ’44 the Polish officers ‘Gwido Langer and Maksymilian Ciezki confess to the Germans that the Enigma cipher was broken before the war’. However there is no reference to this event in the war diary of Inspectorate 7/VI, at least in the files I have.
Unanswered questionsFrom the information presented so far it is clear that in 1939 the Germans were able to find proof that their Enigma cipher machine had been read by the Poles. However it doesn’t seem like they were able to conclusively identify the Polish methods of solution. In any case they correctly dropped the double encipherment of the indicator in 1940, thus defeating the main Polish method of solution. During the war they continued to investigate case ‘Wicher’ but unfortunately we do not know what kind of information they got from interrogating the Polish officers. Buggisch said in TICOM report I-92, p5 that when Dr Pietsch (head of the mathematical research department of Inspectorate 7/VI) interrogated the two Polish officers in 1944 ‘he did not bother to get the details of the Polish method’. This seems nonsensical and it’s possible that Buggisch either did not know more on the subject or was trying to mislead his interrogators.
In any case the people they interrogated could not have told them what they really needed to know, mainly that the British codebreakers could solve daily keys through the use of ‘cribs’ and high speed cryptanalytic equipment.The Germans certainly did not think that the Enigma was unbreakable and they continuously upgraded its security from the 1930’s till the end of the war (7). Regarding their investigations on the theoretical solution of the machine so far we know that the Army codebreakers wrote several reports on how the internal settings could be retrieved under different sets of circumstances (8). In 1944 the naval cryptanalyst Frowein showed that the 4-rotor Enigma could be solved on a crib of 25 letters (9).
Unfortunately with different agencies investigating the security of the Enigma and with their reports scattered across different government archives it is difficult to reach a conclusion regarding their investigations. It is up to researchers to locate and study the relevant reports so a conclusion can be reached regarding the German knowledge of possible solution methods for the Enigma. Notes:
(1). Der Fall WICHER: German Knowledge of Polish Success on ENIGMA(2). ‘Decrypted Secrets Methods and Maxims of Cryptology’, p118
(3) The Journal of Intelligence History article: ‘The Admiralty And Cipher Machines During The Second World War: Not So Stupid After All’, p3(4). Der Fall WICHER: German Knowledge of Polish Success on ENIGMA, p3-4
(5). TICOM reports I-78, I-92, I-127, I-200(6). Intelligence and National Security article: ‘Signals intelligence and Vichy France, 1940-44: Intelligence in defeat‘, p184: ‘According to Bertrand, between October 1940 and November 1942, 'Cadix' decoded 673 Wehrmacht and 3,097 police and SS transmissions pertaining to France and occupied Europe. Bertrand subdivides these decrypts into Wehrmacht Enigma transmissions, police and SS messages, Abwehr agents' instructions and reports, and Armistice Commission signals encoded manually.’
(7). Enigma security measures(8). TICOM DF-190 series reports
(9). TICOM I-38 ‘Report on interrogation of Lt. Frowein of OKM/4 SKL/III, on his work on the security of the German naval four-wheel Enigma’↧
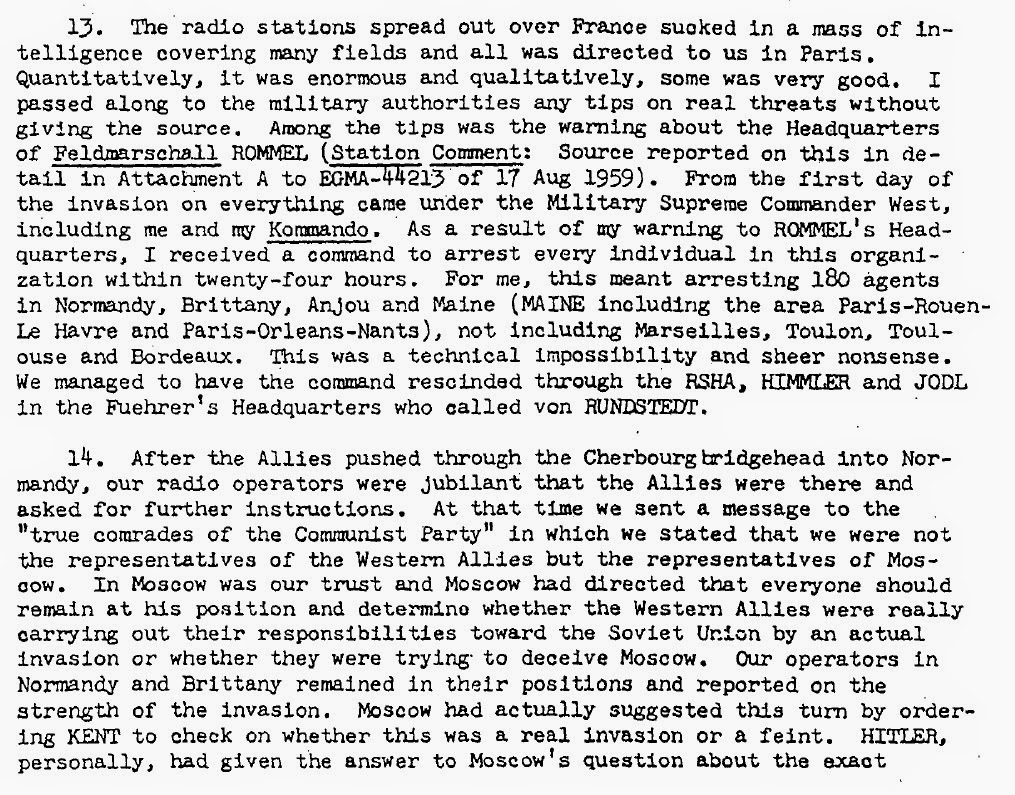
The French War Ministry’s FLD code
In May 1940 Germany shocked the world by defeating the combined forces of France, Britain, Belgium and Holland in a short land campaign. Unlike World War I that had ended in millions of deaths and a stalemate in the West, this time the German forces were able to quickly defeat their opponents. After France’s defeat several theories were promoted, trying to explain this strange outcome. Some focused on the supposed superiority of the Germans in manpower and armaments, while others tried to point to the German Panzer divisions that supposedly had a big advantage over the similar French units.
The code of the French War Ministry
This success was accomplished by the codebreakers of the German High Command's deciphering department – OKW/Chi. Wilhelm Fenner, who was head of the cryptanalysis department of OKW/Chi, said in TICOM DF-187B, p7
Among his conclusions about this case were that a country should not adopt for its main cipher a system that is already known to the enemy and thus possibly compromised and that indicator groups should be independent of the cipher.
General Gamelin who commanded the French forces told Churchill that the defeat was due to: ‘Inferiority of numbers, inferiority of equipment, inferiority of method’. In fact both sides had roughly similar strength in troops and aircraft while in tanks it was the Franco-British alliance that had the advantage, both in terms of numbers and of quality.
However the German were able to overcome their tank inferiority by grouping their armored divisions together, supporting them with ample airpower and providing them with dedicated infantry, anti-tank, artillery and communication units. At the same time their radio communications system was much more advanced than the French Army’s and orders could be dispatched quickly and securely to all units.The German leadership also took a big risk by attacking through the Ardennes area with the purpose of cutting off the northern part of the Allied front.
Another area where the Germans had the advantage was in signals intelligence. Unfortunately historians have focused almost exclusively on the German Enigma cipher machine and its solution by the codebreakers of Bletchley Park thus neglecting the many successes of the German codebreakers. The German victories during the period 1939-1942 in France, N.Africa, Atlantic and in the Eastern Front were achieved at least in part thanks to their ability to read their enemies communications.
French military codes and the Battle of FranceThe French military and civilian authorities used for their secret communications several codebooks, both enciphered and unenciphered. Individually these systems did not have a very high degree of security but it seems that the French strategy was to overwhelm enemy codebreakers through the simultaneous use of a large number of different codebooks. (1)
In addition to the codebooks a number of Hagelin B-211 and C-36 cipher machines had been ordered in the 1930’s. These cipher machines proved secure in 1940 but it doesn’t seem like they were available in large numbers since the codebooks continued to be used on important French communications links.From recently released TICOM reports and various books it is clear that the Germans could read French Army tactical codes (2), the Navy’s main cipher system (3) and the Airforce’s ‘Aviation Militaire’ (4). By exploiting these systems the Germans obviously got valuable intelligence. However their main success that directly contributed to their victory in 1940 was achieved against a high level enciphered code used by the French War Ministry.
The code of the French War Ministry
From the early 1930’s the German codebreakers could read the code used between the French War Ministry and the various military districts. This was a 4-figure codebook of 10.000 values enciphered with additive sequences. In September 1939 there was a change in the method of encipherment and columnar transposition was used instead of addition. Unfortunately for the French this method had been used by one of their military districts prior to September 1939, thus allowing the Germans to solve it and figure out how the transposition keys were chosen. Thanks to this compromise the Germans could read messages of the War Ministry and the military districts till June 1940. The information gained concerned the French army’s order of battle, the weak point of the Maginot Line, the mood of the troops and the population in France and in the colonies, the order of battle of the British troops stationed on the mainland and their movements.
Information on the compromise of the FLD code is available from several sources.Colonel Mettig, head of the German Army’s signal intelligence agency Inspectorate 7/VI in the period 1941-43, said in TICOM report I-128 ‘Deciphering Achievements of In 7/VI and OKW/Chi’, p2
‘In assessing the value of Signals Intelligence PW considers that the deciphering of messages of strategic importance is more valuable than deciphering those of tactical importance. He therefore rates most highly the solution of the French ciphers in the FLD military network radiating from Paris. The deciphering of this traffic before and during the war gave a clear picture of the order of battle of the French and Belgian armies and also of the British army.’This success was accomplished by the codebreakers of the German High Command's deciphering department – OKW/Chi. Wilhelm Fenner, who was head of the cryptanalysis department of OKW/Chi, said in TICOM DF-187B, p7
‘Even before the military action with France began, the military systems of French higher staffs were solved. This was a 4 or 5-figure code that was systematically transposed (tableau carve) .In the cryptograms a few parallel passages (repetitions) were discovered .The interval between these passages was constant and must therefore correspond to the width of the transposition box as cryptanalytic studies have shown.If I am not mistaken the keys (Loesungen ? ? ? ) ? ? the box itself were taken from the same code book. Despite all the cunning of this cryptographic system, the occurrence of short parallel passages proved fatal. By the aid of these deciphered messages tabs could be kept on the French Army far back into the homeland.’
Colonel Randewig, head of the intercept organization in the West during the 1940 campaign wrote in the report FMS P-038 ‘German radio intelligence’:
‘As early as December 1939 the Germans broke a special cryptographic system used by the French command in radio messages to the armies and military district headquarters. It had been used contrary to regulations prior to the opening of hostilities in September 1939. The Germans were able to solve this system because the radio station guilty of the violation was reprimanded and thereupon repeated the same messages in the proper system. Their contents revealed a certain amount of organizational information, for example, the fact that the French 2d and 3d Cavalry Divisions had been reorganized into the 1st and 2d Armored Divisions and were due to move into their assembly area northeast of Paris by 1 January 1940. However, this type of incomplete information could generally be considered only as a supplement to and confirmation of other intelligence concerning the enemy. It was not possible to deduce the enemy's order of battle from radio intelligence alone.Nevertheless, the Germans could identify the probable concentration areas of the French and British armies from the practice messages sent by the field radio stations, although the boundaries of army groups, armies, corps and divisions could not be established with any certainty. Greater clarity prevailed about the fortified area behind the Maginot Line in the south. Enemy forces stationed near the Frenco-Swiss and Franco-Italian borders were not observed according to any regular plan. Spot-check intercepting failed to pick up the French Tenth Army in the place where it was presumed to be by the German command. However, radio intelligence did indicate the presence of the French Sixth Army.’
The importance of this intelligence is even admitted by the official history ‘British Intelligence in the Second World War volume 1’, p163-4‘It later became clear that, until the fall of France, Germany enjoyed not only the strategic initiative but also the advantage of good operational intelligence……….During the planning and the carrying out of the attack on France the work of the enemy intelligence department of the General Staff of the German Army was of crucial importance and its value fully justified the prestige which the department had always enjoyed. The work has been described by General Ulrich Liss, head of the department from 1937 to 1943. He emphasizes that partly on the basis of British army documents captured in Norway, which provided all it needed to know about the British order of battle, and partly from the cypher traffic between the French War Ministry and the army groups, armies and home authorities, most of which it read from soon after the outbreak of war until 10 May, the department had a very comprehensive and accurate knowledge of the dispositions and qualities of the Allied forces…………During the campaign its intelligence continued to be good, and Sigint continued to be the best source.’
However the person who can give the most accurate account of the work done on the FLD code was the chief cryptanalyst of OKW/Chi, Erich Hüttenhain. According to Hüttenhain’s manuscript ‘Einzeldarstellungen aus dem Gebiet der Kryptologie‘, p14-16 the code used between the French War Ministry and the military districts was a 4-figure codebook of 10.000 values, enciphered with short additive sequences. Since this method of encipherment offered limited security and the underlying code remained in use for years these messages could be read by the Germans. However a different system was used by the military district in the border with Italy. Here the code was transposed based on codewords. After finding two messages with parallel passages the German codebreakers were able to solve this system in 1938 and they realized that the transposition keys were created by using the codegroups of the codebook. Thus from mid 1939 the traffic of this military district could also be solved. In September 1939 when WWII broke out the French War Ministry instead of changing the cipher procedures, ordered that this system of transposition was to be used by all the military districts. Since the 4-figure codebook remained in use the Germans could read this traffic up to June 1940 and Hüttenhain says that the German leadership was informed of all significant operations within the French armed forces.Among his conclusions about this case were that a country should not adopt for its main cipher a system that is already known to the enemy and thus possibly compromised and that indicator groups should be independent of the cipher.
’Das französische fld-Netz
Beim Anfang der dreißiger Jahre benutzte das französische Kriegsministerium im Verkehr mit den französischen Wehrkreisen zur Verschlüsselung der Nachrichten einen 4Z-Code, der mit einer endlichen Additionszahl überschlüsselt wurde. Fast alle 10.000 Gruppen des 4Z-Codes waren belegt. Der Code wurde im Laufe der Jahre nicht geändert oder gar abgelöst. Die Additionszahlen wurden in kürzeren Zeitabschnitten abgelöst. Es waren jeweils gleichzeitig mehrere Additionszahlen im Gebrauch. Die Längen der einzelnen Additionszahlen waren ungerade und schwankten zwischen 7 und 13 Ziffern. Die mit dieser Geheimschrift,also mit dem 4Z-Code verschlüsselten Nachrichten wurden in den letzten Jahren vor dem 2. Weltkrieg vollständig mitgelesen. In dem Verkehr mit dem an Italien angrenzenden französischen Wehrkreis verwendete das französische Kriegsminister rium ein anderes Chi-Verfahren. Im vorangehenden Studium des gesamten Spruchmaterials dieses einen Verkehrskreises wurden 2 Sprüche gefunden, die eine größere Anzahl von fast gleich langen und über die ganzen Spruchlängen fast gleichförmig verteilten Ziffernfolgen enthielten; lediglich die Reihenfolge der diese 2 Anfangszeilen bildenden Ziffernfolgen in den beiden Sprüchen war verschieden. Diese Feststellung führte zur Erkenntnis, daß ein Ersatzverfahren mit einem Würfel überschlüsselt wurde. Mit Hilfe von 2 Anfangsreihen konnte die Würfellosung rekonstruiert und das Ersatzverfahren als 4Z-Code erkannt werden.-Es war also in den beiden Sprüchen, die zum Einbruch in das Verfahren führten, eine längere, sich über mehrere Zeilen des Würfelkastens erstreckende gleiche Textstelle vorhanden. Der 1. Einbruch gelang im Jahre 1938. Im Laufe der nächsten Monate wurden weitere dieser Parallelstellen-Kompromisse gefunden. Es wurden die in Wortlosungen umgewandelten Würfellosungen als die Klarbedeutungen der Codegruppen des verwendeten 4Z -Codes erkannt. Und es wurde erkannt, da als Kenngruppen für die Würfellosungen 4Z -Gruppen des Codes gewählt wurden, deren Klarbedeutung jeweils die Wortlosung des Würfels war. Auf diese Weise lieferten gedeutete Codegruppen neue Würfellosungen und rekonstruierte Würfellosungen neue Codegruppen. Mitte 1939 wurde der gesamte Verkehr zwischen dem französischen Kriegsministerium und dem an Italien angrenzenden Wehrkreis, der also mit der Geheimschrift 4ZCüW verschlüsselt wurde, mitgelesen.
Als am 3. September der Krieg mit Frankreich ausbrach, verfügte das französische Kriegsministerium, daß die bisher nur im Verkehr mit dem an Italien angrenzenden Wehrkreis benutzte Geheimschrift 4ZCüW unverzüglich auch in allen anderen Wehrkreisen verwendet wurde. Es blieb der Code derselbe, und es wurden die Würfellosungen nach wie vor aus den Klartextbedeutungen der Codegruppen genommen. Es wurden lediglich an den jeweils folgerden Monatsersten geringfügige Änderungen an den Kenngruppen vorgenommen, Änderungen, die in kurzer Zeit erkannt und nach einigen Wechseln sogar vorausgeahnt wurden. Dieser Zustand blieb bis zum Ende des Frankreichfeldzuges im Juni 1940 unverändert bestehen. Jeder aufgenommene Spruch dieses militärischen Führungsnetztes, das als fld-Netz bekannt war, wurde mitgelesen. Die deutsche militärische Führung war über alle wesentliche Vorgänge innerhalb der französischen Wehrmacht unterrichtet. Neben der Gliederung in der französischen Wehrmacht klärten die mit gelesenen Sprüche die Bewaffnung der einzelnen Einheiten auf, die schwächste Stelle der Maginot-Linie, die Stimmung der Truppe und der Bevölkerung in Frankreich und in den Kolonien, die auf dem Festland stationierten englischen Truppen und deren Bewegungen usw.
Es erscheint angebracht, an Hand dieses für Frankreich und für Deutschland folgenreichen Entzifferungs ergebnisses einige Folgerungen zu ziehen: 1. Es ist falsch, ein Chiffrierverfahren, dessen Sicherheit nicht bewiesen ist, zum Hauptverfahren zu machen, wenn es bereits als Nebenverfahren als beim Gegner bekannt vorausgesetzt werden muß.
2. Ein Chiffrierverfahren, dessen Sicherheit von der Struktur der Klartexte-Anfängen, Schlüssen, Parallelstellen, Spruchlängen u.a. - abhängig ist darf nicht verwendet werden. 3 Kenngruppen müssen vom Chiffrierverfahren unabhängig sein; sie dürfen keine doppelte Bedeutung haben.
4. Die Erfassung des Spruchmaterials sollte vollständig sein, um auch die kompromittierenden Sprüche finden zu können.Anm.: Rekonstruierte Seite einer Kopie, deren 12 Anschläge links unlesbar waren. Hier sind also die ersten 12 Anschläge erraten,-allerdings sinngemäß! Ausnahme: Zeile 12, wo die Zahl 13 willkürlich ist,für die allerdings 2 Bedingungen stehen: 1) >7 und Zweistelligkeit (in den 12 Anschlägen).’
ConclusionThe German victory in the Battle of France shook the world in 1940 and countless theories were formed in order to explain this unusual event. Up to 1940 the French Army was thought to be the most powerful and best equipped force in Europe. Supported by the small British Expeditionary Force, the powerful British Fleet and with military supplies coming in from the United States the Franco-British alliance had every reason to expect a victory over Germany thanks to its superior economic resources.
The German leadership took a huge gamble by concentrating all their armored divisions and using them to encircle and destroy the northern flank of the Allies but this gamble paid off. In a victory of such magnitude it is not possible to attribute success to only one factor. Obviously the German advantages in training, doctrine, leadership, communications etc were decisive. However the German victory also owed a lot to signals intelligence and codebreaking. Especially the solution of the War Ministry’s code gave the Germans valuable information on the location of the Allied units and was obviously used during the planning stage for the attack. Notes:
(1). TICOM report DF-187B, p6 (2). EASI vol1 – ‘results of European Axis cryptanalysis’
(3). ‘Delusions of intelligence: Enigma, Ultra and the end of secure ciphers’, p44(4). TICOM report I-112, p6
↧
↧
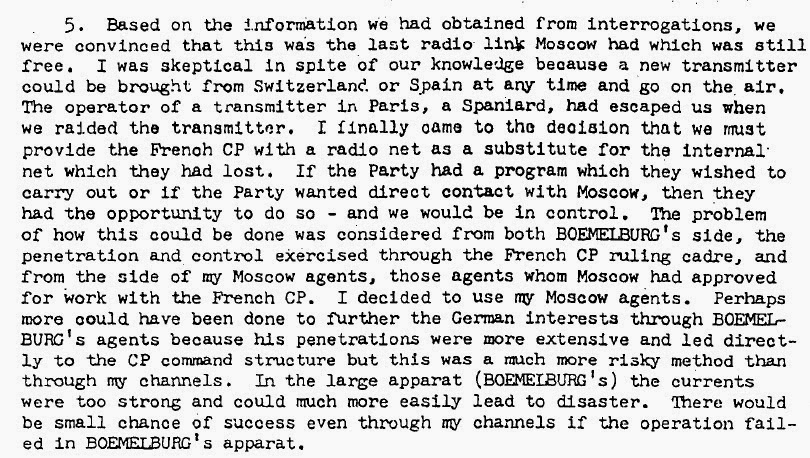
Compromise of Soviet codes in WWII – the good, the bad and the unexpected
After covering the cryptologic failures of the United States and Britain in WWII, i’m currently writing a summary of the compromise of Soviet codes in WWII, however there are some good news and some bad news regarding the available sources.
The good news
The war diary of the German Army’s signal intelligence agency Inspectorate 7/VI and the reports of the cryptanalytic centre in the East Horchleitstelle Ost (later named Leitstelle der Nachrichtenaufklärung) are available for the period 1941-43. Also summaries on the solution of Soviet codes are available for the period October 1944-March 1945.The bad news
I haven’t been able to find the reports of Horchleitstelle Ost for the second half of 1941 and for the period February- September 1944.The unexpected
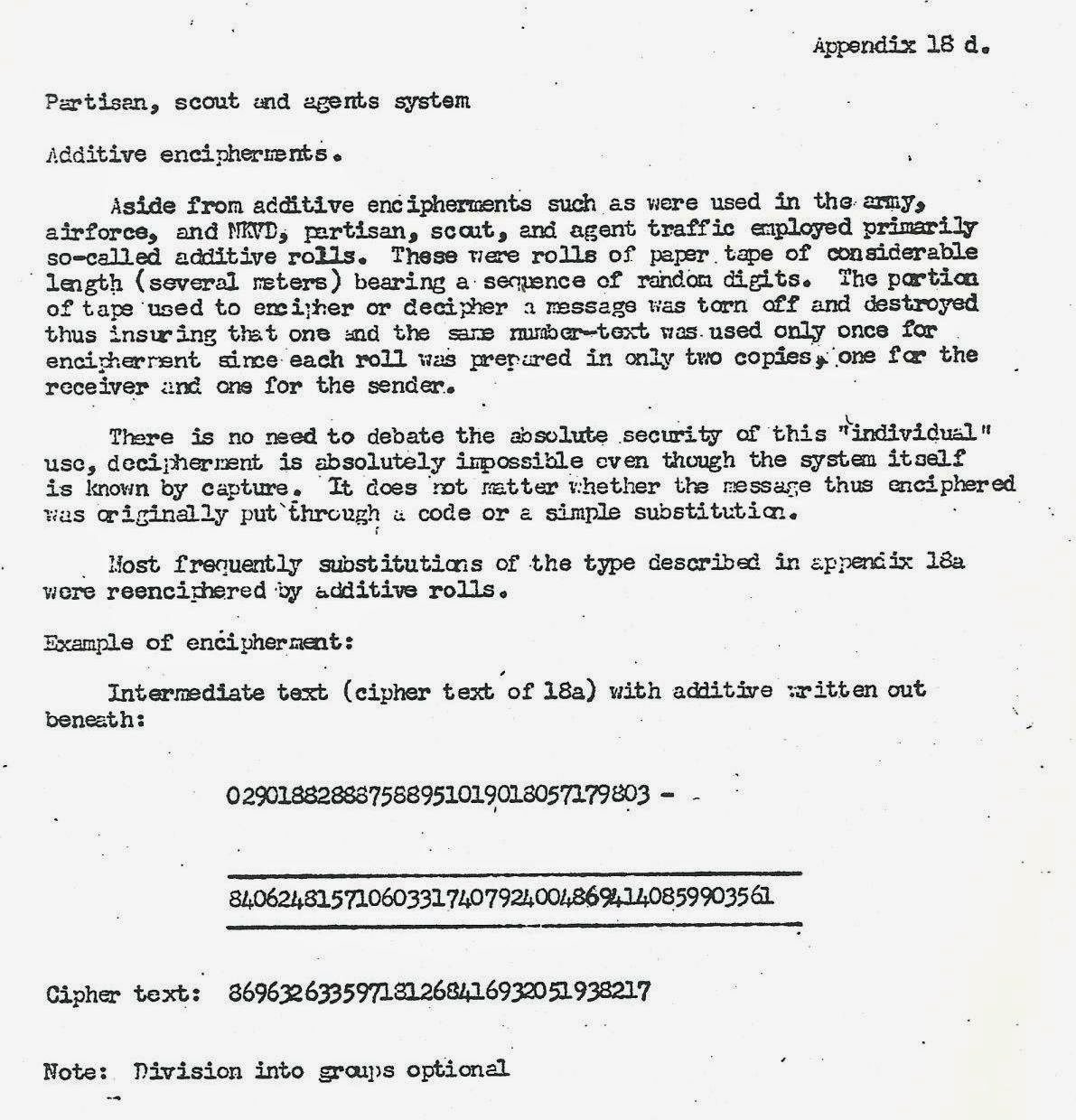
According to a recently declassified TICOM report the Germans were able to read the first version of the Soviet diplomatic one time pad code in the 1930’s and the codes of the Comintern. In the first case their success was due to the fact that the system was not true one time pad in that one additive page was assigned to each message. If the values were not enough to encipher the entire message then they were reused.In the case of the Comintern it seems that the main system used by Communist Parties around the world was a numerical code used together with a letter to number substitution table. The table was used as a ‘key’ generator for additive sequences used to encipher the coded message. A common book would be used for this purpose and the user would identify through the indicator the page and line that the sequence would start from. In one such case the Germans solved the ‘encipherment sequence of about five million digits’ and identified the five books used as cipher.
↧
Update
I have uploaded TICOM report DF-105 ‘Determination of the Absolute Setting of the AM-1 (M-209) by Using Two Messages with Different Indicators’. Acquired through the NSA’s FOIA office.
Available from my Google docs and Scribd accounts.
Available from my Google docs and Scribd accounts.
↧
Update
I have uploaded TICOM report DF-111 ‘Comments on various cryptologic matters’. Acquired through the NSA’s FOIA office. Available from my Google docs and Scribd accounts.
I have rewritten Soviet Diplomatic Code 26 and the elusive Dr Roeder using information from DF-111.
I have rewritten Soviet Diplomatic Code 26 and the elusive Dr Roeder using information from DF-111.
↧
Compromise of Soviet codes in WWII
Signals intelligence and codebreaking played an important role in WWII. British and American codebreakers solved many important Axis crypto systems, such as the German Enigma machine and the Japanese Navy’s code JN25.
Regarding the 4-figure traffic, up to 1942 a 4-figure codebook OKK (General Commander’s Code) was used. The codebook had 50 pages of 100 groups each for a total of 5.000 code groups, arranged alphabetically (6). Encipherment was by means of substitution tables.
In mid 1942 the use of the OKK codes was discontinued and instead units were given authorization to create their own 4-figure substitution tables called SUW/SUV. Based on guidelines from the Army’s cipher department each unit had permission to create its own 4-figure code table and the enciphering method.
Examples of SUV tables (7):
NKVD codes
Partisan codes
Diplomatic codes
Foreign intelligence and Comintern codes
The monthly reports of HLS Ost, together with TICOM reports written by personnel assigned to work on the solution of Soviet codes show that Soviet military 2, 3 and 4-figure codes were continuously read, with new systems being solved each month. Soviet AF traffic seems to have been easier to solve than the Army’s since more traffic was generated daily as the air units had to use the radio much more often than their Army counterparts.
Things changed in the summer of 1941 when due to the military operations the Soviet communication system broke down, leading to mistakes in encipherment and in addition codebooks were captured by the Germans. This led to the solution of even the high level Soviet communications, carried out between the General Staff and the Fronts. A summary from August 16 1941 says that since the beginning of the war with Russia (ie, for a period of about 2 months) 69 cipher procedures had been resolved and one of the greatest successes of the unit included the solution of the 5 figure additive procedure RC 130, which could be read already 6 days after the war started. This system was used by the Soviet General Staff and conveyed information on the most important commands and operational messages.
The files I have do not include the reports of HLS Ost for the second half of 1941 or January 1942 but the report from February shows that the 5-figure code could still be exploited revealing orders for operations, situation reports, reconnaissance reports, information on troop movements, inventory of ammunition and food, reports of desertion etc
In the first half of 1942 use of the 5-figure codes started to expand, reaching roughly 50% of intercepted traffic. Also a new 5 figure code 023-A replaced the previous 011-A (used in 1941 and early 1942). The codebreakers of HLS Ost were able to solve 5-figure traffic in this period but the use of ‘Individual’ additive pads for a lot of the traffic meant that the analysis of this material had to be undertaken at headquarters in Berlin, using the IBM/Dehomag punch card equipment in order to find repeats.
The high level 5-figure traffic was using mainly ‘Individual’ additive pads, so only a small number of messages seem to have been read. Also in 1943 the new 5 figure code 045-A was used till midyear. Then the 062-A was used by the Army.
In the same period the important RC 1100 code (original name 039W) was investigated and code values recovered. Report of June ’43
In July the code of NKVD counterintelligence RC 1500 was read revealing operations against German parachutist agents.
In August the fourth main NKVD cipher procedure RC 1510 was listed as solved and in September work on the NKVD 4-figure methods RC 747, RC 1100, RC 1500, RC 1510 was making good progress. In the same month the NKVD railway code RC 1560 could be read continuously.
NKVD codes continued to be read with success up to end 1944 since these systems seem to have remained in use for long periods of time. For example the Germans expected that the important RC 1100 code of 10.000 values would be changed in January 1944, thus negating their efforts to solve it. However their report of October 1944 says that it was only replaced in September ‘44.
Partisan codes
(3). DF-112, pages 129-165
(13). DF-112, p115
(21). TICOM I-25, p2-5
(23). TICOM I-153, p3: ‘In Autumn 1944 both the end of 'adder' and every pause in the cipher proper was preceded by seven key letters [redacted]. Then the traffic went off the air and reappeared in December with no external change except that the seven ‘residue' letters had been reduced to three, suggesting a modification of the machine.
Historians have not only acknowledged these Allied successes but they’ve probably exaggerated their importance in the actual campaigns of the war.
Unfortunately the work of the Axis codebreakers hasn’t received similar attention. As I’ve mentioned in my piece Acknowledging failures of crypto security all the participants suffered setbacks from weak/compromised codes and they all had some successes with enemy systems. Britain, the Soviet Union and the United States did not have impenetrable codes. In the course of WWII all three suffered setbacks from their compromised communications.
After having dealt with the United States and Britain it’s time to have a look at the Soviet Union and their worst failures. Move along comrade, nothing to see here
Compromises of communications security are usually difficult to acknowledge by the countries that suffer them. For example since the 1970’s countless books have been written about the successes of Bletchley Park, yet detailed information on the German solution of Allied codes only started to become available in the 2000’s when TICOM reports and other relevant documents were released to the public archives by the US and UK authorities.In Russia the compromise of their codes during WWII has not yet been officially acknowledged and the archives of the codebreaking organizations have remained closed to researchers. This is a continuation of the Soviet policy of secrecy.
The Soviet Union was a secretive society and information was tightly controlled by the ruling elite. This means that history books avoided topics that embarrassed the regime and instead presented the officially sanctioned version of history. Soviet era histories of WWII avoided references to codes and ciphers and instead talked about ‘radio-electronic combat’ which dealt with direction finding, traffic analysis and jamming (1).After the fall of the Soviet Union several important government archives were opened to researchers and this information has been incorporated in new books and studies of WWII. However similar advances haven’t taken place in the fields of signals intelligence and cryptologic history. Unlike the US and UK that have admitted at least some of their communications security failures the official line in Russia is that high level Soviet codes were unbreakable and only unimportant tactical codes could be read by the Germans. Even new books and studies on cryptology repeat these statements (2).
However various sources such as the TICOM reports, the war diary of the German Army’s signal intelligence agency Inspectorate 7/VI and the monthly reports of the cryptanalytic centre in the East Horchleitstelle Ostclearly show that the Germans could solve even high level Soviet military and NKVD codes. Overview of Soviet cryptosystems
The secretive Soviet state used various cryptosystems in order to secure its communications from outsiders. The task of preparing and evaluating cipher procedures was handled by two main Soviet organizations, the NKVD’s 5th Department and the Army’s 8th department of the main intelligence directorate GRU. In the 1920’s simple substitution systems were used and these were solved by codebreakers in Poland (Polish-Soviet war of 1919-21) and in Britain (ARCOS case). In the 1930’s the communications of units in the Far East were read by the Japanese codebreakers and during the Soviet-Finnish war of 1939-40Soviet codes were read by the Finns with disastrous consequences for the Soviet armed forces.
The basic cryptologic systems used by the military, the diplomatic service and the security services during the period 1941-45 were the following:1). The Soviet military used 2, 3, 4 and 5-figure codes enciphered with substitution methods or with additive sequences. The latter method was reserved for the most important 4 and 5-figure codes.
2). The People's Commissariat for Internal Affairs - NKVD also relied on figure codes enciphered both with substitution and addition methods.3). Partisan groups used figure codes enciphered with additive sequences or transposed based on a key word.
4). The diplomatic service had a 4-figure codebook enciphered with one time pad tables plus an emergency system.5). The agents of the foreign intelligence service that did not have diplomatic cover and the Communist International mostly used a simple letter to figure substitution table to encode a message and this was further enciphered by using a book and the aforementioned conversion table to create additive sequences.
6). Internal radio traffic between factories and the People's Commissariats of heavy industry, tank production, engineering etc was sent both unenciphered, enciphered with simple cover words or with figure codes and with one time pad tables.7). According to the available sources the Soviet Union relied almost entirely on hand methods for enciphering its important communications. A small number of cipher machines were available but it doesn’t seem that they were used widely during the war. The known types were the K-37 ‘Crystal’ (Soviet copy of the Hagelin B-211) and the cipher teleprinters B-4 and M-100.
8). Voice communications were protected by the EU-2 speech scrambler and the Cobol P device.Military codes
TICOM reports DF-112 ‘Survey of Russian military systems’ (3), DF-292 ‘The Cryptologic Service in WWII (German Air Force)’ (4), IF-175 ‘Searbourne Vol. XIII, PT. 2’ and I-19 a-g ‘Report on Interrogation of KONA 1 at Revin, France, June 1945’ give a summary of the main military cryptosystems. The basic systems were 2, 3 and 4 figure letter/word to figure substitution tables used either unenciphered or enciphered with similar substitution tables. The 2 and 3 figure code tables were used by frontline units, while the 4-figure codes were used at division level and above.
Examples of 2 and 3 figure tables (5):
In mid 1942 the use of the OKK codes was discontinued and instead units were given authorization to create their own 4-figure substitution tables called SUW/SUV. Based on guidelines from the Army’s cipher department each unit had permission to create its own 4-figure code table and the enciphering method.
Examples of SUV tables (7):
For the highest level communications a 5-figure codebook was used, enciphered with additive tables called ‘Blocknots’. There were two main types of tables, the ‘General’ (31 pages with each page having 300 5-digit groups – each page was valid of 1 day regardless of the messages sent) and the ‘Individual’ (50 pages with each page having 60-120 5-digit groups - each additive group could only be used once).
Example of 5-figure code encipherment (8):The NKVD used procedures similar to the Army’s. At the top level an enciphered 5-figure code was used. Several large 4-figure codes (up to 10.000 groups) enciphered with additive tables were also used at a high level. Frontline units used small codebooks (approximately 2.500 values) and code tables similar to the Army’s. (9)
Example of NKVD code table (10):Partisan codes
The Soviet partisans used various enciphering procedures in their radio communications with Moscow. These ranged from simple Caesar ciphers to double transposition, transposition using a stencil and Caesar cipher enciphered with one time pad.
Examples of partisan codes (11):Diplomatic codes
The Soviet diplomatic service used a 4-figure codebook enciphered with one time pad. In addition there was an emergency cipher procedure for consulates that did not have access to new enciphering tables.
Foreign intelligence and Comintern codes
Soviet agents operating ‘illegally’ (with no diplomatic cover) did not have access to a regular supply of enciphering tables so they had to memorize a simple letter to figure conversion table and use it to encode their messages. Then they could also use this table for encipherment by using a prearranged book as a ‘key’ generator. Passages from the book would be taken, the letters would be converted into numbers through the conversion table and this numerical sequence would be used to encipher the message (addition without carrying over the numbers).
The same basic system was used by Communist Parties in their communications with Moscow. A codebook or conversion table would be used to encode the message and a random book would provide the additive sequences as above. (12)
Internal radio traffic
Radio communications between factories, State authorities, civil aviation and military units in the Soviet interior were sent plaintext, encoded with a simple system, using 3 or 4 figure substitution codes or with the Army’s 5-figure code and one time pad tables.German solution of Soviet codes in WWII
The German intercept organization in the East
Codebreaking and signals intelligence played a major role in the German war effort. Army and Luftwaffe units relied on signals intelligence in order to monitor enemy units and anticipate major actions.In the period 1941-45 the Army had 3 signal intelligence regiments (KONA units) assigned to the three Army groups in the East (KONA 3 for Army Group North, KONA 1 for South and KONA 2 for Centre). There was also NAA 11 - Signal Intelligence Battalion, providing intelligence to the German forces in Finland. This unit exchanged results with the Finnish codebreakers.
In 1942 another KONA unit was added to Eastern front and from 1943 mostly monitored Partisan traffic, this was KONA 6.The Luftwaffe had similar units assigned to the 3 Air Fleets (Luftflotten) providing aerial support to the Army Groups. Army and Luftwaffe signals intelligence units cooperated closely and exchanged results on a daily basis.
Both the Army and the Luftwaffe also established central cryptanalytic departments (Horchleitstelle Ost and LN Regt 353) for the Eastern front. The Army’s Horchleitstelle Ost (later renamed Leitstelle der Nachrichtenaufklärung) was based in East Prussia. The signal intelligence regiments had fixed and mobile intercept units plus a small cryptanalytic centre called NAAS (Nachrichten Aufklärung Auswertestelle - Signal Intelligence Evaluation Center). Although they were subordinate to Horchleitstelle Ost, in practice they had significant autonomy on the traffics they chose to cover (13). The task of the field units was to exploit current enemy cryptosystems using the material given to them by their NAAS units and by HLS Ost. New cipher procedures were not supposed to be handled by forward units but instead they were tackled by HLS Ost and the NAAS units. Important Soviet codes such as the Army’s enciphered 5-figure code and the NKVD cryptosystems were handled solely at HLS Ost and by the central department in Berlin.
Apart from the Army’s Inspectorate 7/VI and the Luftwaffe’s Chi Stelle several other organizations also worked on Soviet codes. The Navy’s signal intelligence agency B-Dienst– Beobachtungsdienst had intercept units in the Black Sea and in the Baltic, the Signal Intelligence Agency of the Supreme Command of the Armed Forces OKW/Chihad a Russian department under professor Novopaschenny that worked on the 5-figure code, the Forschungsamtintercepted traffic from the Soviet interior (mostly of economic content), the Foreign Ministry's deciphering deparment Pers Z solved Comintern codes and the Army’s Ordnance, Development and Testing Group, Signal Branch – Wa Pruef 7 Group IV section C intercepted Soviet multichannel radio-teletype traffic from inside the Soviet Union.The German Allies in the East (Italy, Hungary, Romania) did only limited work on Soviet codes. The exception to this rule was Finland, whose codebreaking department had been solving Soviet codes since the 1930’s and continued to do so up to 1944. Relations between Finnish and German codebreakers were close and they exchanged information on important systems.
Overview of German codebreaking successes
The communications of the Soviet Union were a major target of the German codebreakers during the interwar period and several military systems had been solved up to the 1941 invasion (14). The exploitation of these codes from an early date allowed the Germans to follow changes and improvements in Soviet procedures, as simple systems used in the 1920’s and 1930’s were replaced with more complex ciphers. Also the Soviet-Finnish war of 1939-40 served as a training exercise for the German signal intelligence organizations since ample radio traffic from actual fighting units could be intercepted and examined. The occasional mistakes made by Soviet cipher clerks, the large volume of traffic and the cipher material captured by the Finns and shared with the Germans contributed to the solution of most of the Soviet enciphered traffic, including the Army’s high level 5-figure code (15). In the period 1941-45 the German signal intelligence agencies continued to exploit a large part of Soviet military and NKVD 2, 3 and 4 figure codes and even succeeded in solving some of the 5-figure traffic.
Limits of available sources
Unfortunately the files of many of the organizations intercepting and exploiting Soviet codes were either destroyed in WWII or are still classified by the NSA. However the material released to the US, UK and German archives in the last decade is sufficient for evaluating the general performance of German signals intelligence in the Eastern front. The most reliable sources are the monthly reports of Referat 5 and of Horchleitstelle Ost, which are included in the War Diary of Inspectorate 7/VI. These are available for the first half of 1941, for the period 1942-43 but not for January to September 1944 or for the period July 1941 – January 1942 (at least I haven’t been able to find them).
Soviet Army and Airforce codes
The Army’s Inspectorate 7/VI and the Luftwaffe’s Chi Stelle intercepted and decoded Soviet communications through their forward units and from fixed stations in the East. Forward units were supposed to exploit systems that had already been identified and solved. On the other hand new traffic and difficult high level systems were tackled at the cryptanalytic centre Horchleitstelle Ost/Leitstelle der Nachrichtenaufklärung in East Prussia. This arrangement meant that field units could process a lot of messages each month without the need for specialized personnel and the results were quickly communicated to the armed forces. According to TICOM report I-19 (16) the estimated monthly average for KONA 1 (assigned to Army Group South) in 1944 were 5.500 cipher, 6.000 clear text and 500 practice messages for a total of 12.000. The systems exploited by field units were 2, 3 and 4-figure codes. The NKVD systems and the Army’s 5-figure code were processed at HLS Ost.
Prior to the 1941 invasion the Luftwaffe’s Chi Stelle could solve the majority of intercepted Soviet codes (17). The Army agency could also exploit the majority of systems but it was hampered by lack of personnel and the processing of the 5-figure code was slow due to the limited number of messages intercepted daily (18). Still the reports say that the information from signals intelligence was extremely valuable to the General Staff.
Report of period Jan-Mar 1941:Report of 10 June 1941:
Report of 16 August 1941:
Report of HLS Ost - February 1942
Also in 1942 the widely used Army 4-figure codebook OKK was replaced with a large number of SUV substitution tables. Although the security of such a system was not very high the use of different SUV tables by each unit meant that solution depended on the amount of material received and on operator errors.
In 1943 the reports of HLS Ost show that apart from 2, 3 and 4 figure codes also traffic from the Soviet interior was intercepted and solved.Report of July 1943
The reports of January-September 1944 are missing but those of October ’44 - March ’45 show that military codes continued to be solved. The new 5-figure code 091-A could only be read in rare cases.
Reports of Referat 2 - October 1944Soviet Navy codes
The German Navy’s signal intelligence agency B-Dienst monitored the Soviet naval traffic in the Black Sea, the Baltic and the North Sea. Low level systems used by small ships were continuously read and high level 4-figures codes could also be exploited till late 1943. An important success for the German side was the solution of the simple codes used by Soviet naval aircraft in the North Sea. This traffic carried important information on the convoys between the UK and the SU. Thanks to this information the Germans were able to inflict significant losses on these convoys.
NKVD codes
The People's Commissariat for Internal Affairs - NKVD was a huge organization tasked with foreign intelligence, internal security, border security, railroad security and overview of the state run economy. The communications of such an important organization were targeted by the German codebreakers and traffic from NKVD border units could be read in the 1930’s (19). During WWII there was a separate department at Horchleitstelle Ost for NKVD traffic. NKVD codes were extensively read, not only 2 and 3-figure codes used by frontline units but also several large 4-figure codebooks used by higher authorities(GUP NKVD-General Directorate of Border and internal security and Front staffs).
By reading these communications the Germans got intelligence on the operations of the NKVD border units, the conditions in the Army’s rear areas were the NKVD was responsible for security, intelligence operations, railway shipments and even reports on the Soviet economy. The reports of HLS Ost list many NKVD systems solved in 1942, 1943 and 1944. For example in April ’42 5-figure traffic was solved (since the NKVD also used the army’s 011-A and 023-A codes) and the code N.17 of the 23rd NKVD Railway division.
In June 1942 the codes 06-Pand N.14 are mentioned:
In January the new code 010-Pwas solved after discovering the enciphering procedure.
Partisan codes
Partisan codes were investigated by Inspectorate 7/VI’s Referat 12 (Agents section) in 1942 and by signal intelligence regiment 6 -KONA 6 in the period 1943-44.
The reports of Referat 12 for the second half of 1942 show that partisan communications were monitored and the different types of traffic were classified by the cipher system used. However, apart from a few spy cases, actual traffic was not solved.List of Russian agents and partisans traffics from October 1942:
In 1943 KONA 6 was assigned to cover partisan traffic and from summer 1943 some of it could be read. The results were communicated to the security services like the Abwehr so that enemy agents could be apprehended and partisan operations thwarted.
Comintern codes
The codes of the Comintern were read by the Foreign Ministry's deciphering department Pers Z. According to Adolf Paschke (20), head of the linguistic cryptanalysis department, different books were used in order to create cipher sequences and encipher the underlying code but thanks to human error it was possible to solve these and identify the books used. Apparently the personnel that were responsible for enciphering messages had the tendency to reuse specific passages from the books thus compromising the whole system. Paschke said that ‘A particular instance deserves mention. It concerns telegraphic material of a total length of about two million digits. In the course of the work of solution it was established that it had been enciphered by means of five books which gave an encipherment sequence of about 5 million digits. An apparently hopeless case. And yet solution was achieved’.Diplomatic codes
The Soviet diplomatic service used a 4-figure codebook enciphered with one time pad tables. In the Far East a simpler procedure was also used, probably due to the lack of new enciphering tables. According to German accounts they monitored Soviet diplomatic traffic but could not solve messagesdue to the use of one time tables. Internal network
State ministries, factories and military units in the Soviet interior relied on radio communications for a lot of their traffic because the landline network was not fully developed to cover the huge areas of the Soviet Union. 1). Economic traffic between factories was intercepted and solved by the Forschungsamt (21). According to Paetzel (head of department 6 - Cipher Research), traffic from the SU averaged several hundred messages per day and was mostly plaintext with cover words. The chief evaluator Seifert said: ‘Our greatest success was obtained on Internal Russian traffic which enabled us to discover the various bottlenecks in the Russian supply organization’. A British report on the Forschungsamt says that the communications of several Soviet Commissariats (tank industry, munitions, machine tools etc) were read (22):
2). The civil aviation network’s 3 figure code was read by Army codebreakers since summer 1943.
Report of June ’43:3). Apart from standard radio communications there were also multichannel radio teletype devices being used. The Germans were able to intercept these transmissions automatically and print the text. Economic traffic was often sent plaintext while military communications used 3, 4 and 5 figure codes. The 3 and 4 figures could be read.
Cipher machines
At this time there is very limited information on WWII era Soviet cipher machines.
1). The Germans captured a K-37 machine in the summer of 1941, examined it and came up with methods of solution. However during the war they did not intercept any messages enciphered on this device, so it seems that it was not used in the Western areas of the SU. 2). Apart from the K-37, two cipher teleprinters were identified by the Germans. Both seem to have had 6 wheels with five enciphering the respective Baudot impulses while the sixth controlled their movement. One of these was solved by cryptanalysts of the Forschungsamt in 1943 and the other was continuously monitored by the Army codebreakers in the period 1943-45. The available reports have no information on the Forschungsamt solution and exploitation of this traffic.
Regarding the second device the war diary of Inspectorate 7/VI shows that the traffic was continuously examined and some progress was made thanks to operator errors and a flaw in the construction of the machine (23). This device was used on communications links between Moscow and the Army Fronts. There were only about 10 links overall with ~8 for the Army and ~2 for the Airforce (24). Although the machine was not ‘broken’, messages in depth could be decoded and they contained reports on Soviet and German military dispositions, , statements by POW's, signal intelligence reports, reports for TASS and SOVINFORMBUREAU, letters concerning postings, transfers, promotions, weather situation reports and supply manifests (25).3). Radio fax transmissions were intercepted and decoded, however no information is available on the type of cipher device used on this traffic by the Soviets. The traffic contained hand-written communications, typewritten texts, drawings, weather maps, technical diagrams and charts.
4). Speech privacy systems were used for radio telephone conversationsbetween Moscow and various cities such as Leningrad, Irkutsk, Alma Ata and Chelyabinsk. The Germans were able to solve the first Soviet device but no information is available on the traffic they intercepted or its contents. The second device introduced during the war was more secure and although German specialists identified it as a Tigerstedt system (time division scrambling) it was not ‘broken’.Failures of Soviet cipher security
The Soviet Union had failed to secure its sensitive communications during the 1920’s and 1930’s. In 1920 the victory of the Poles over the Red Army in the battle of Warsawowed a lot to the work of their codebreakers. In the 1930’s Soviet military codes were read by the Japanese in the East and by the Finns during the Winter war. In 1941 the sudden German attack destroyed a large part of the Soviet military and their communications system collapsed. The loss of trained radio operators and of cipher material meant that Soviet communications were extensively read by the Germans. Moreover the new hastily trained radio operators could not avoid making mistakes and thus compromising the security of otherwise secure systems.
However the widespread use, during the war, of 2, 3 and 4 figure code tables enciphered with substitution methods was a mistake considering that they could only offer limited security. Especially for the 4-figure mid and high level communications a more secure procedure should have been adopted. Obviously the fact that they could be easily used by hastily trained personnel must have played a role in this case.Another lost opportunity was the lack of a secure cipher machine for widespread usage among the armed forces. Such a device would have a allowed a large volume of traffic to be sent quickly and securely. The Soviets used cipher machines in very small numbers and only in a handful of communication links.
Other mistakes noted by the Germans were that the operational plans of units using secure procedures were compromised by smaller units supporting them such as artillery, rocket launcher, heavy mortar and engineers since these did not use secure procedures. The NKVD was guilty of using insecure codes and also of keeping their codebooks in use for long periods of time, thus making the work of the German codebreakers much easier.
The biggest failure of the Soviet cipher departments was their unwillingness to acknowledge their failures and introduce new secure procedures. According to Anatoly Klepov (26), in the postwar era there was an evaluation of Soviet cipher security during WWII and although it was acknowledged that their codes had been compromised the final report hid this fact in order to protect the reputation of Lavrentiy Beria, head of the NKVD. This mistake meant that outdated codes and procedures continued to be used in the immediate postwar period and they were exploited by Anglo-American codebreakers in the years 1945-48, when they managed to solve many important Soviet cryptosystems, including the top level cipher teleprinters.
Conclusion
The use of signals intelligence and codebreaking by the Germans and Soviets in the Eastern front is a subject that has received very little attention by historians so far. The main reason was the lack of adequate sources. The archives of the Soviet codebreaking organizations remain closed to researchers but in the last decade many important documents on German signals intelligence operations have been released to the public archives. From these documents it is clear that the Germans invested significant resources in their signal intelligence agencies and relied on their output during the fighting in the East. Against an opponent that outnumbered them in men and war materiel (tanks, planes, artillery) signals intelligence gave them the opportunity to monitor enemy movements and make efficient use of their limited resources.
The cryptologic systems used by the Soviet Union at low and mid level were extensively compromised during the war and in 1941-42 even their high level 5-figure code could be read. In the period 1943-45 the use of one time pad in enciphering their 5-figure code secured this system but other important codes could be read including the systems of the NKVD.The report FMS P-038 ‘German radio intelligence’ says ‘In the Russian theater the mass of minute details assembled by German communication intelligence over a period of years provided a clear, reliable, and almost complete picture of the military potential, the strategic objectives, and the tactical plans of the most powerful enemy which the German Army had ever encountered. The results were far superior to those obtained during World War I’.
Considering the countless enemy cryptosystems solved by the Germans during the period 1941-45 (military, NKVD, partisan, economic) this statement does not appear to be an exaggeration. Notes:
(1). Journal of Contemporary History article: ‘Spies, Ciphers and 'Zitadelle': Intelligence and the Battle of Kursk, 1943’, 249(3). DF-112, pages 129-165
(4). DF-292, pages 53-86
(5). DF-292, p 54-55 and DF-112, p129-30(6). DF-112, p151-52
(7). DF-112, p143-44, p153-54(8). DF-112, p157
(9). Reports of HLS Ost(10). DF-112, p155-56
(11). DF-112, p158-63(13). DF-112, p115
(14). DF-112, p170-86
(15). IF-175 ‘Searbourne Vol. XIII, PT. 2’, p23(16). I-19b, p44
(17). DF-292, p24-29(18). Reports of Referat 5 January-June 1941.
(19). DF-112, p7-22(21). TICOM I-25, p2-5
(23). TICOM I-153, p3: ‘In Autumn 1944 both the end of 'adder' and every pause in the cipher proper was preceded by seven key letters [redacted]. Then the traffic went off the air and reappeared in December with no external change except that the seven ‘residue' letters had been reduced to three, suggesting a modification of the machine.
(24). TICOM I-153, p2
(25). TICOM I-169, p25↧
↧
Svetova Revoluce and the codes of the Czech resistance
At the end of the First World War the multiethnic Austro-Hungarian Empirecollapsed and out of its ruins emerged several new countries. One of these was Czechoslovakia, containing the Czech areas of Bohemia and Moravia together with Slovakia and Carpathian Ruthenia in the east.
In the interwar period Czechoslovakia followed a foreign policy supportive of France and was part of the Little Entente. The country had a stable democracy and its industrial resources were large (based on the Skoda works) for such a small country. However there were two important problems affecting Czech national security. On the one hand the rise of Nazi Germany and its rearmament was a clear security threat. At the same time there were serious problems with the German and Slovak minorities that resented Czech rule.
Czechoslovakia contained a large number of minorities that were dissatisfied with the ruling Czech establishment. Especially the German minority made up roughly 23% of the population (according to the 1921 census) and a large part of it was concentrated in the border with Germany called Sudetenland. Many of the Sudeten Germans wanted for their areas to be unified with Germany and in the 1930’s Hitler’s Germany supported the demands of the Sudeten German Party. These claims were rejected by the Czech government of Edvard Beneš and as the Czech crisis threatened Europe with a new war a conference took place in Munich between the governments of Germany, Italy, Britain and France.
More information on this case is available from the reports of department 12 (Referat 12) of the German Army’s signal intelligence agency Inspectorate 7/VI(1). Referat 12 was tasked with the solution of agent’s codes and during the war they were able to solve many crypto systems from agents of every Allied country.
1) General:
The cooperation with Ag WNV / Fu III aJ continued as to be as active as before. On 21.10. Oblt. Vauck traveled to Prague with two men from the Department to clear and remove the deciphering difficulties of the messages on the lines 9 and 11 of the Czech mbm network. Meetings with the Abwehrstelle (Abwehr branch) Prague (Captain Dr. von Breitenberg ), Gestapo ( Kriminalrat Schulze ) and Order Police resulted in: The 12 key books indicated on the basis of earlier agent interrogations do not come into question.
By purely analytical deciphering work the first entry in the latest messages of the Czech line 11 was achieved, with that new, extensive message collections have been made accessible for treatment. The main credit for this falls to Uffz Rossiwal and Fu. (Funker – radio operator) Haubrich. At the same time the cipher documents of the captured parachutist group 'A', the solution of this complicated cipher system: 2-digit Caesar + columnar transposition, additionally super-enciphered.
In the interwar period Czechoslovakia followed a foreign policy supportive of France and was part of the Little Entente. The country had a stable democracy and its industrial resources were large (based on the Skoda works) for such a small country. However there were two important problems affecting Czech national security. On the one hand the rise of Nazi Germany and its rearmament was a clear security threat. At the same time there were serious problems with the German and Slovak minorities that resented Czech rule.
Czechoslovakia contained a large number of minorities that were dissatisfied with the ruling Czech establishment. Especially the German minority made up roughly 23% of the population (according to the 1921 census) and a large part of it was concentrated in the border with Germany called Sudetenland. Many of the Sudeten Germans wanted for their areas to be unified with Germany and in the 1930’s Hitler’s Germany supported the demands of the Sudeten German Party. These claims were rejected by the Czech government of Edvard Beneš and as the Czech crisis threatened Europe with a new war a conference took place in Munich between the governments of Germany, Italy, Britain and France.
Without support from Britain and France the Czech government was forced to cede the Sudeten territories to Germany and also lost other disputed areas to Hungary and Poland. Even though Germany had succeeded in absorbing the Sudeten areas and in weakening Czechoslovakia that did not stop Hitler’s offensive plans and in March 1939 German troops invaded and occupied the rest of the country. From then on the country was ruled by Germany and special attention was given to its heavy industry which produced weapons for the German armed forces.
During the war the Czech Government in Exile, headed by Beneš, was based in London and had regular communications with the Czech resistance. The most daring operation of the resistance was the assassination of Reinhard Heydrich, protector of Bohemia and Moravia and former head of the Reich Main Security Office. However after this episode the Germans took many security measures and were generally able to keep the resistance activities under control. In this area they took advantage of the insecure communications between the resistance and the Czech intelligence service, operating from Britain.Referat 12 and the Czech MBM network
The solution of Czech resistance codes is mentioned in TICOM report I-115‘Further Interrogation of Oberstlt METTIG of OKW/Chi on the German Wireless Security Service (Funkuberwachung)’, p8. This report was written by colonel Mettig, head of the German army’s signal intelligence agency in the period 1941-43. According to Mettig the communications between Britain and Czechoslovakia were read by the Germans and they contained reports on the political situation and the operations of the Czech resistance.
The monthly reports show that the codes of the Czech resistance (called mbm network) were investigated in 1942 and in the period October-December they were finally solved.
In October there was a meeting in Prague between the head of Referat 12, dr Vauck and Abwehr, Gestapo and Ordnungspolizei officials. Thanks to information gathered by their agents it was possible to identify some of the books used to encipher the Czech messages. One of these was ‘Svetova Revoluce: Za Valky a ve Valce 1914-1918’ by Tomáš Masaryk (founder and first President of Czechoslovakia). Some messages were solved at the Vienna Postal censor office (Ausland Brief Prüfstelle) by one of their agents.Report of October 1942
The cooperation with Ag WNV / Fu III aJ continued as to be as active as before. On 21.10. Oblt. Vauck traveled to Prague with two men from the Department to clear and remove the deciphering difficulties of the messages on the lines 9 and 11 of the Czech mbm network. Meetings with the Abwehrstelle (Abwehr branch) Prague (Captain Dr. von Breitenberg ), Gestapo ( Kriminalrat Schulze ) and Order Police resulted in: The 12 key books indicated on the basis of earlier agent interrogations do not come into question.
The agents’ statements in these and other points do not correlate. The books were left at the Prague Abwehr branch. The from now on designated as relevant key books are: Masaryk, Svetova revoluce ; General Inger’s Letter; some magazine numbers - were not known neither at Ag WNV / Fu nor In 7/VI.
Useful decryption information, which should have been in the records of the Order Police, had been sent to Vienna and there given to a V-man (agent) Emil for processing of the messages. Berlin offices have not received these documents. Instead of the V-man called back to Prague came, after one and a half day’s wait and due to a misunderstanding in Vienna, another agent.A long distance call to V-man Emil in Vienna ABP (Ausland Brief Prüfstelle – Postal censor office) revealed that he had been able to decipher some of the messages on line 9. The system turned out to be correctly known here . The Vienna V-man is still working on breaking into the double transposition of the line 11, which is difficult work for a single individual due to the number of the necessary attempts. Information about the key books and their monthly relevant page numbers as well as the useful key documents given to Vienna, should rapidly be sent from Vienna to here via the Prague Abwehr branch.
Prague will send the Masaryk book. In summary, it is clear that important and useful documents have not been sent here but to Vienna, whereby the examination and processing of the material was complicated and delayedIn November there were more meetings with officials in Prague and an agreement was reached on cooperation between Referat 12 and the Vienna Postal censor office. A notable success was the discovery of secret records in a notebook of the resistance member Josef Louzecky, a native of Neumeritz. However these were enciphered so they had to be analyzed and solved.
Report of November 1942
General:
Cooperation with Ag WNV / Fu III aJ continuous actively. To further clarify the cipher procedures in the Czech mbm - network the Head of Unit met earlier this month in Prague with the clerk of the State Police Prague. Significant details were finalized already there and finally at a second meeting at the Ausland Brief Prüfstelle (ABP - Postal Censor Office)in Vienna around the 20th this month. Their knowledge allowed here the first successful break in line 9 of the Czech resistance movement. In a meeting chaired by the head of the Vienna ABP, lieutenant colonel von Gross, the guidelines for further cooperation in the form of a working group with the cipher specialists of censor office laid down. Again, the personal agreement proved to be conducive to the tasks of the Unit.
…………………………………………………………
In the messages of line 9 of the Czech mbm network a first successful break was made. 32 messages were solved. Through the acquisition of more extensive material from the central office of the radio intercept service of the Order Police further possibilities of penetration by decoding are given. The monthly change of key books or poem keys that are never transmitted over radio certainly complicate the ongoing deciphering; but suitable compromise cases will help. Also here the collaboration with the ABP in Vienna will prove to be beneficial. A rare task lay ahead with the secret records in a notebook of the Czech Josef Louzecky, a native of Neumeritz. These are encrypted by a character Caesar. By a kind of shorthand reshuffling and further transformation of the initial characters a more complicated cipher is produced. With skillful choice of the attack points a successful break was made. The transformation in clear text will take some days to complete, but promises a lot of essential information, including addresses.In December the messages of the period April-September 1942 were solved and also the diary of Josef Louzecky, revealing ‘a considerable number of names, addresses and important information’.
Report of December 1942
Eastern networks: The messages of line 9 of the Czech mbm network has now from April to September 1942 been broken. Unteroffz. Rossiwal has discovered important changes in the Caesar construction and furthermore the origin of the daily indicator. The processing of all the material is done essentially by him.
………………………………………..
The secret records in the notebook of Czech agents Louzecky deciphered Uffz Schreier as homophonic character Caesar. The complete decryption yielded a considerable number of names, addresses and important information.In 1943 and 1944 messages continued to be deciphered, even when the cipher was changed. The cipher systems mentioned in the reports were:
1). 2-figure code plus double transposition of the digits using a book as a generator for the transposition keys.2). 2-figure code enciphered with repeating 10-figure sequence.
3). 2-digit code with columnar transposition, additionally super-enciphered.Report of January 1943
The messages of line 9 of the Czech mbm networks are now broken by decipherment for the whole year of 1942. In the last two months more than 300 messages of the year have been deciphered, the rest will be done in the first weeks of February. A material of smaller size with no indicator groups – supposedly operational messages – has been split into the here known and practiced system: double transposition and afterwards 2-digit Caesar substitution. The deciphering will, due to the existing compromises, be possible at the earliest moment.
At line 11 new messages with a four-fold over-ciphering of the basic Caesar have arrived; they will be attacked by line 11 in the course of their processing.Report of March 1943
The main method seems to have been the 2-figure code with double transposition. This means that the letters of the alphabet would be assigned a 2-digit equivalent (A=56, B=39, C=04, etc). Then the message would be encoded using this system and the result would look like a random sequence of numbers. This sequence would be further enciphered with the double transposition system, using ‘key’s taken from a prearranged book. The indicator of the message would let the other party know which page and line of the book was chosen as a ‘key’. In theory this system was quite secure but in practice it was solved by the Germans.
Overall a significant amount of Czech messages were solved in the period 1942-February 1944 (last month of available Referat 12 reports).Jan ’43 - 300
May ’43 - 366June ’43 - 431
July ’43 - 309August ’43 - 215
Sept ’43 -196Oct ’43 - 111
Nov ’43 - 134Dec ’43 - 249
Feb ’44 - 262Swedish effort
The Germans weren’t the only ones that were able to exploit Czech codes in WWII. Sweden remained neutral during the war but its signal intelligence service FRA - Försvarets Radioanstalt was able to solve many foreign codes and ciphers, including the early models of the German Siemens and Halske T52 cipher teleprinter.The famous mathematician Arne Beurling was responsible for this success and also for the solution of other cryptosystems. One of the systems solved by the Swedish codebreakers was the double transposition code used by the Czech intelligence service (2). In the period 1939-42 the former Czech embassy counselor Vladimír Vaněk was living in Sweden and he collected information on political and military development through his friends and acquaintances in Stockholm. Vaněk had regular talks with important individuals such as government ministers and even the private secretary of Prime Minister Per Albin Hansson.
This information was then sent in code to the Czech government in Exile, based in London. His messages had the indicator CXG and were actually transmitted by the British embassy in Stockholm. The Swedes had been intercepting this traffic since 1940 and after an extensive cryptanalytic attack were able to ‘break’ the system and read most of the traffic of the period August 1941-March 1942. In March 1942 the house of Vladimír Vaněk was raided and the Swedes searched for incriminating evidence, including a ‘big red book’ that he had mentioned in one of his decoded messages. They did find it and it was indeed red but not really big. This was the book used to create the transposition keys. It’s name? Svetova Revoluce…
Notes:
(1). War diary of Inspectorate 7/VI(2). ‘Codebreakers: Arne Beurling and the Swedish Crypto Program During World War II’, chapter ‘The double transposition’
Acknowledgements: I have to thank Frode Weierud for translating the Referat 12 reports.
↧
Compromise of OWI - Office of War Information communications
In 1942 the US government created a new organization called the Office of War Information, headed by Elmer Davis. This organization absorbed the functions of several other government departments such as the Office of Facts and Figures (OWI's direct predecessor), the Office of Government Reports, the Division of Information of the Office for Emergency Management and the Foreign Information Service.
The OWI had representative in countries abroad and participated not only in news gathering activities but also Anti-Axis propaganda and even espionage. Especially in Bern, Switzerland the local station, headed by Gerald Mayer, cooperated closely with the OSS -Office of Strategic Services station of Allen Dulles.
The book ‘Hitler, the Allies, and the Jews’, p265 says about Mayer:‘Gerald Mayer was officially OWI’s man in Bern but in fact he was Allen Dulles’s cover and right hand man’
The same book mentions an OWI message from Mayer to Elmer Davis from May 1944, decoded by the German codebreakers. The Germans were not the only ones reading OWI communications from Bern. The Finnish codebreakers also read these messages, as can be seen from a decode found in the Finnish national archives:
Bern-Washington 9.3.1944 No.1438 (to Elmer Davis OWI from Mayer)↧
Sonderkommando Rote Kapelle and the radio network of the French Communist Party
The Soviet Union was a secretive state convinced that the capitalist world was plotting to invade and destroy it. In order to avert such a development the Soviet government financed and organized the creation of spy networks throughout Europe. These penetrated military, economic, political and diplomatic circles. Many of the agents were devoted communists who thought they were working for the creation of a better world.
However after exposing and dismantling these networks the Germans took measures to continue their transmissions to Moscow, so that they could pass false information to the Soviets and also receive information on new spies sent to the West.
These stations had been located by the Germans and they were eliminated thus preventing direct communications with Moscow. However Pannwitz knew that eventually the communists would replace these stations with new ones and risk exposing his operations in France. In order to preempt such a move the Sonderkommando established a new French CP radio network that was in reality under its complete control.
Using the cover of the Rote Kapelle, the resistance leader Paul Victor Legendre was persuaded to set up this radio network. The Germans managed to build up this organization and inserted their own men as radio operators. By operating this network they got a large number of daily espionage reports and were able to keep track of the resistance and stop acts of sabotage.
The operations of the network concluded in the summer of 1944 when the Germans had to evacuate Paris. Till that time however the German intelligence agencies got information of great value through the French CP radio network.
Germany was a major target of the Soviet spies, especially after power was seized by the NSDAP party. The Red Orchestra was the name given by German intelligence to the Soviet spy networks operating in Europe during WWII. These networks had been set up in the 1920’s and had managed to infiltrate government departments and business circles of every country in Europe. Through their spying activity they kept Moscow informed of important events in Europe.
Their means of communication was the radio and it was this means that led to their downfall. The German Radio Defence agency (Funkabwehr) was able to locate one of the sites used for radio transmissions in 1941 and by apprehending the cipher clerks and their cipher material they were able to read this traffic.By decoding messages they uncovered the names of many Rote Kapelle members and of course these were arrested, interrogated and more people were incriminated. By late 1942 the main networks in Western Europe were destroyed.However after exposing and dismantling these networks the Germans took measures to continue their transmissions to Moscow, so that they could pass false information to the Soviets and also receive information on new spies sent to the West.
The unit tasked with dismantling the Rote Kapelle networks and handling the radio deception (funkspiel) was the Sonderkommando Rote Kapelle,headed in 1943-44 by Heinz Pannwitz.
Operations Eiffel and Mars
In the period 1943-44 the Sonderkommando Rote Kapelle/ Sonderkommando Pannwitz was based in Paris and handled the radio-games between captured Soviet agents and Moscow. The Germans had managed to capture the leaders of the organization Leopold Trepper (Grand Chef) and Anatoly Gurevich (Petit Chef).After a short period in captivity Trepper managed to escape but Gurevich was used by the Germans to report disinformation to Moscow and convince them that their spy networks were operating normally.
Radio messages were sent from Paris (operation Eiffel) and from Marseille (operation Mars). The radio network of the French communist party
Another success of the Sonderkommando Rote Kapelle concerned the undercover radio network of the French communist party. According to a recently declassified CIA report, written by Pannwitz, the French CP had prepared a network of undercover radio stations, ready to be used when the party leadership ordered it. Using the cover of the Rote Kapelle, the resistance leader Paul Victor Legendre was persuaded to set up this radio network. The Germans managed to build up this organization and inserted their own men as radio operators. By operating this network they got a large number of daily espionage reports and were able to keep track of the resistance and stop acts of sabotage.
According to Pannwitz an added benefit of running this network was that during the Normandy campaign some of the radio stations continued to transmit information, this time on the strength and operations of the Allied forces.
Sources: CIA Report - PANNWITZ, HEINZ VOL. 2_0042, CSDIC/CMF/SD 80 - 'First Detailed Interrogation Report on LENTZ, Waldemar, and KURFESS, Hans'
↧
Update
I have rewritten French Hagelin cipher machines.
↧
↧
Wired magazine interviews Edward Snowden
↧
Upcoming essays
I think that I’ve covered practically all the important cryptologic cases of WWII in my current essays. In order to write more I’ll need access to files that the NSA is in the process of declassifying and that may take a while. However there are two stories that I’m going to cover in the future. One concerns the German research on the British Typex cipher machine and the other will be a summary of the work of the Agents section of the German Army’s signal intelligence agency.
Typex
Many authors claim that the German codebreakers had a look at the British Typex cipher machine and then gave up because they considered the task hopeless. Apparently that was not true for the German army’s codebrealers:
Referat 12
Referat 12 (Agents section) of the German Army’s signal intelligence agency OKH-Inspectorate 7/VI dealt with the codes and ciphers of enemy agents. During the war they solved the cryptosystems of British, French, Belgian, Polish, Czech, Russian, Greek, Bulgarian and Norwegian spies and saboteurs. A summary of their work during the period May 1942- February 44 (last available reports) is in order.↧
Update
↧
Not quite true…
During WWII the top Allied officials in the US and the UK frequently communicated via a radio-telephone link protected by the Bell Labs A-3 speech scrambler. This device was not secure enough to be used at such a high level but since no other alternative was available it was used extensively by military personnel, diplomats and even Roosevelt and Churchill.
In order to secure these sensitive communications the Americans designed and built the Sigsaly device. The NSA website says about Sigsaly:
‘The SIGSALY system was inaugurated on 15 July 1943 in a conference between London and the Pentagon (the original plan had called for one of the terminals to be installed in the White House, but Roosevelt, aware of Churchill's penchant for calling at all hours of the night, had decided to have the Washington terminal moved to the Pentagon with extensions to the White House and the Navy Department building.) In London, the bulk of the SIGSALY equipment was stored in the basement of Selfridges Department Store, with an extension to Churchill's war room, approximately a mile away……….. With the coming of SIGSALY, the shortcomings of the less than effective A-3 were now a thing of the past’. This doesn’t appear to be the whole truth. While it is true that the system was installed in July 1943 it didn’t work properly till late 1943 and it only become fully operational in April 1944. Even after it was installed officials continued to use the A-3 for most of their communications since the only Sigsaly link was available at the Cabinet War Rooms and only a small number of officials had authorization to use it.
This information comes from the book ‘The woman who censored Churchill’, p112-3. I’ve added this information in Intercepted conversations - Bell Labs A-3 Speech scrambler and German codebreakers and German intelligence on operation Overlord.↧
↧
Update
I have added information from the War diary of Inspectorate 7/VI and KONA 4 in The secret messages of Marshall Tito and General Mihailović.
↧
For Victor from Burns
In the period 1942-45 the Office of Strategic Services station in Bern, Switzerland (headed by Allen Dulles) collected information from occupied Europe and transmitted intelligence reports back to Washington. Some of these reports were decoded by the German and the Finnish codebreakers.
The following message can be found in the Finnish national archives. The original was copied from NARA, collection RG 59.
‘Umberto’ may have been Crown Prince Umberto of the House of Savoy.
I have added this messageinAllen Dulles and the compromise of OSS codes in WWII.
The following message can be found in the Finnish national archives. The original was copied from NARA, collection RG 59.
I have added this messageinAllen Dulles and the compromise of OSS codes in WWII.
↧
Update
I have added new messages in Compromise of OWI - Office of War Information communications.
↧
More Pages to Explore .....